Our modern backup solution goes beyond file copies—delivering encrypted, immutable data protection that’s air-gapped from your network. Shield your data from ransomware, eliminate reinfection risk, and enable near-instant recovery so your business never skips a beat.
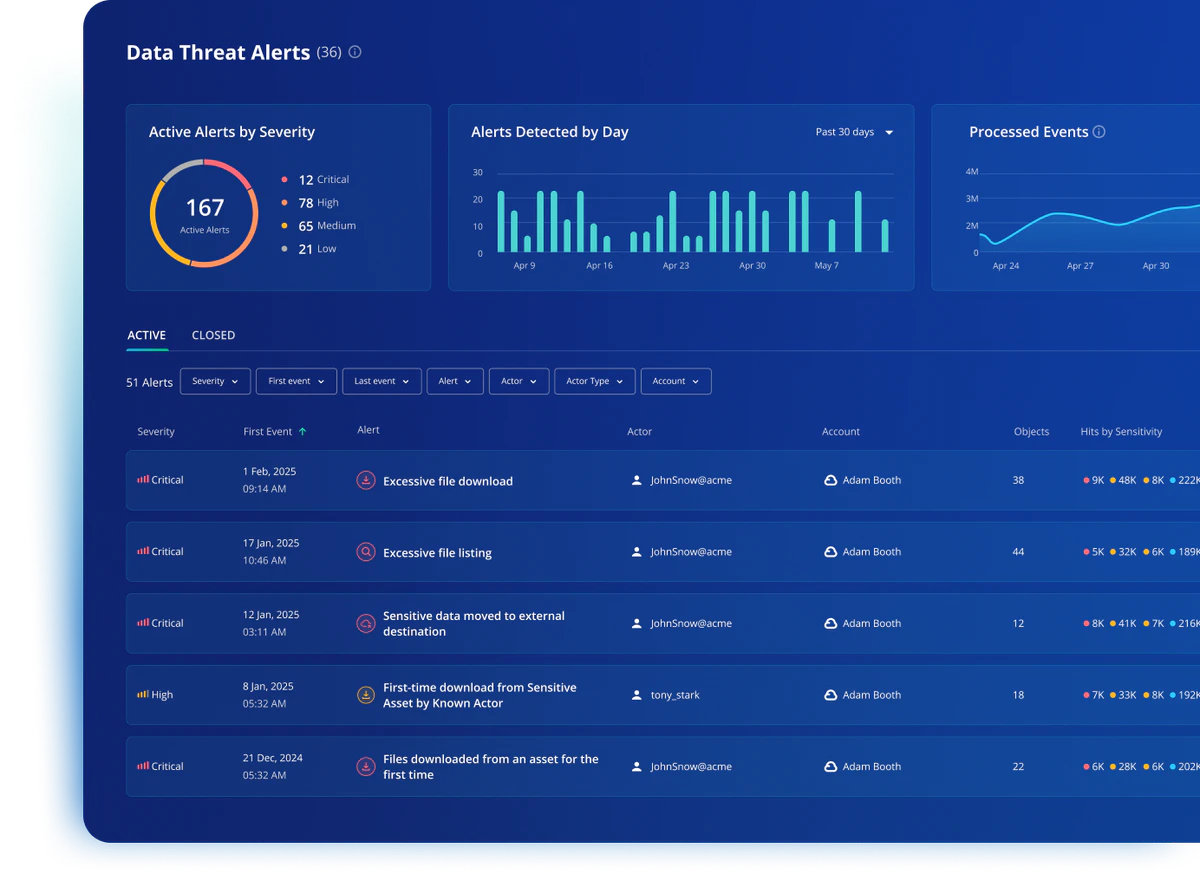
Security isn’t static. Our backup platform not only detects ransomware and anomalies in real time — it locks down data with immutable, air-gapped storage and enables clean recovery in minutes.
Real-time, incremental backups ensure your data is always up to date — with no disruption to daily operations.
All backups are securely stored in geo-redundant data centers, protecting against physical damage or onsite failure.
Keep the data you need, for as long as you need it — with fully customizable backup schedules.
Restore files, systems, or entire environments within minutes to minimize downtime and data loss.
Your data is encrypted both in transit and at rest, meeting strict industry security requirements.
We proactively monitor backup status and notify you of any issues — so you’re always in control.
Real-time, incremental backups ensure your data is always up to date — with no disruption to daily operations.
All backups are securely stored in geo-redundant data centers, protecting against physical damage or onsite failure.
Keep the data you need, for as long as you need it — with fully customizable backup schedules.
Restore files, systems, or entire environments within minutes to minimize downtime and data loss.
Your data is encrypted both in transit and at rest, meeting strict industry security requirements.
We proactively monitor backup status and notify you of any issues — so you’re always in control.
Recover in minutes — not hours — during cyberattacks, hardware failures, or natural disasters. Our Rubrik-powered backups ensure your team stays online, compliant, and ahead of the competition.

Meet and exceed FFIEC, GLBA, and NCUA standards with immutable, air-gapped backups that are ransomware-proof. Automated audit trails and reporting make passing exams faster and less stressful.
Cut storage expenses by up to 40% with intelligent cloud tiering and lifecycle automation. Reclaim IT budget to invest in innovation — without sacrificing security or compliance.

“IMS has become one of our key business partners, and I would recommend IMS without hesitation to anyone seeking to work with a knowledgeable, service-oriented company whose staff truly cares about their clients.”
Heather Ebaugh
VP of Information Systems, Del-One (Delaware FCU)
Fill out the form below to set up a free risk assessment for your organization.
Get the Free Ransomware Recovery Guide